Popular
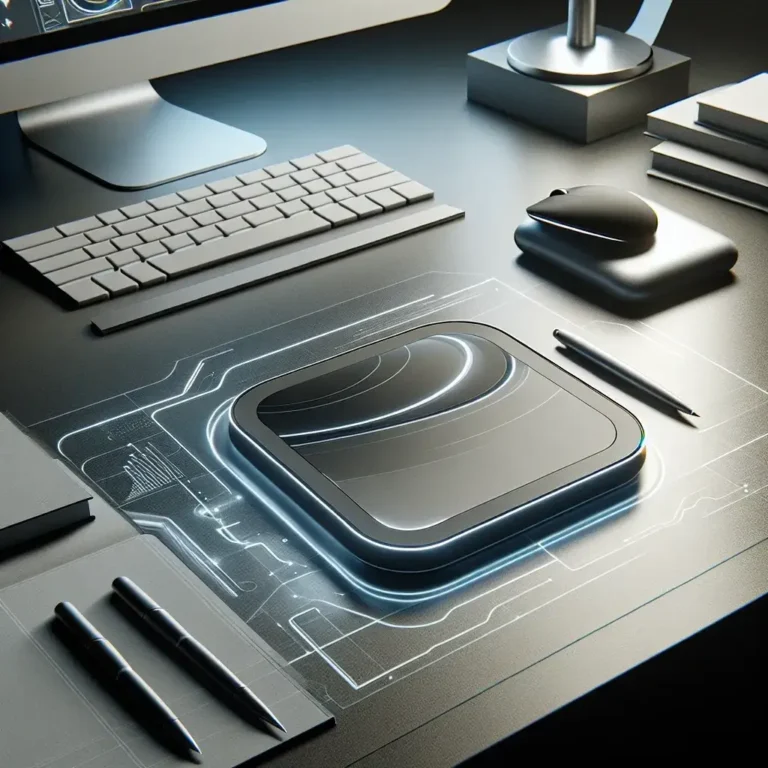
In the ever-evolving world of computer storage, hybrid drives, or
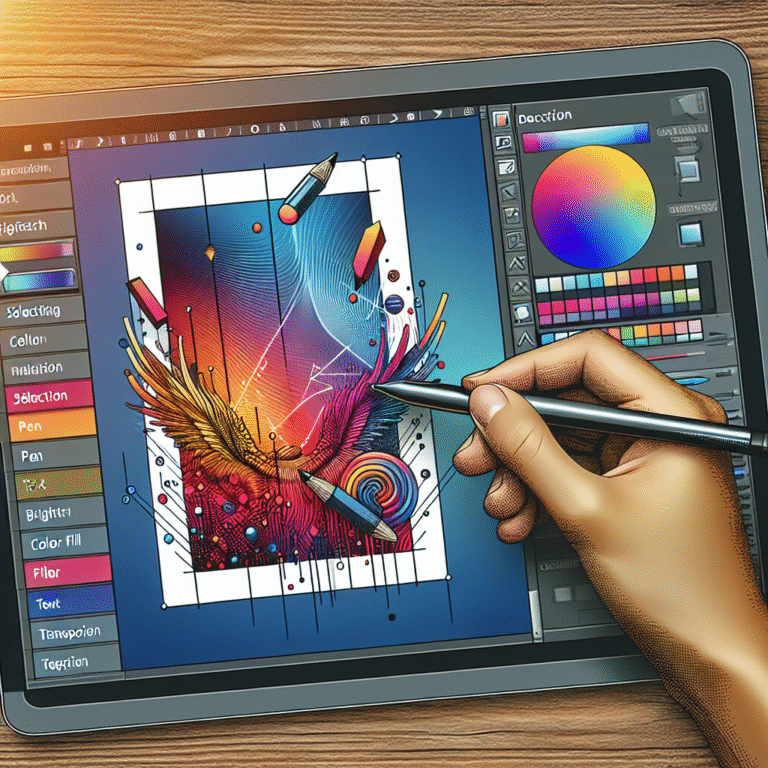
Adobe Illustrator is a powerful tool that is widely used
When it comes to experiencing immersive audio, nothing quite beats
L’intelligence artificielle (IA) révolutionne progressivement tous les secteurs d’activité, et
Twitter Spaces, the platform’s live audio feature, has opened doors
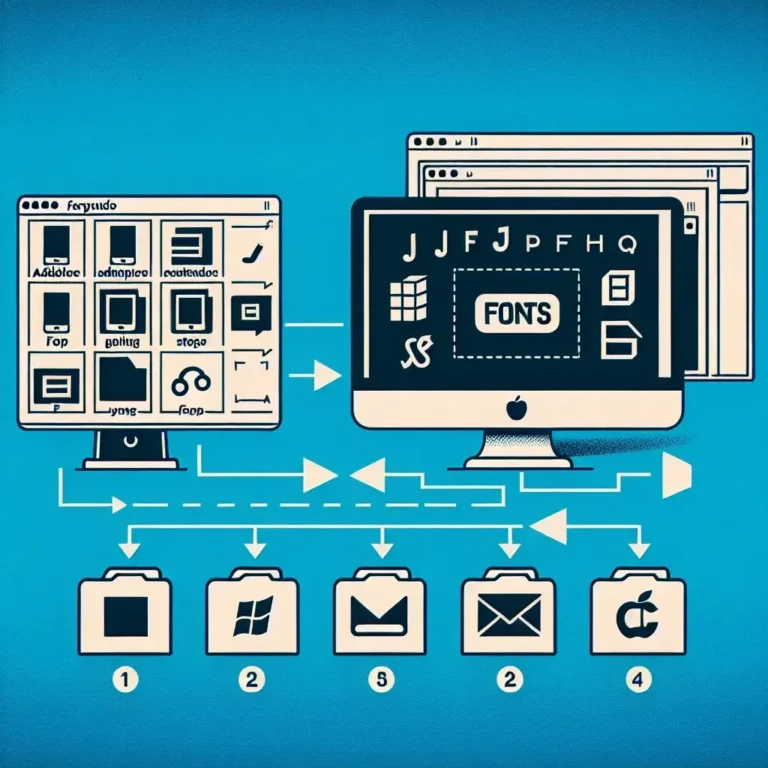
Scheduling the first comment on your Instagram posts is a
Are you looking to enhance the sound quality of your
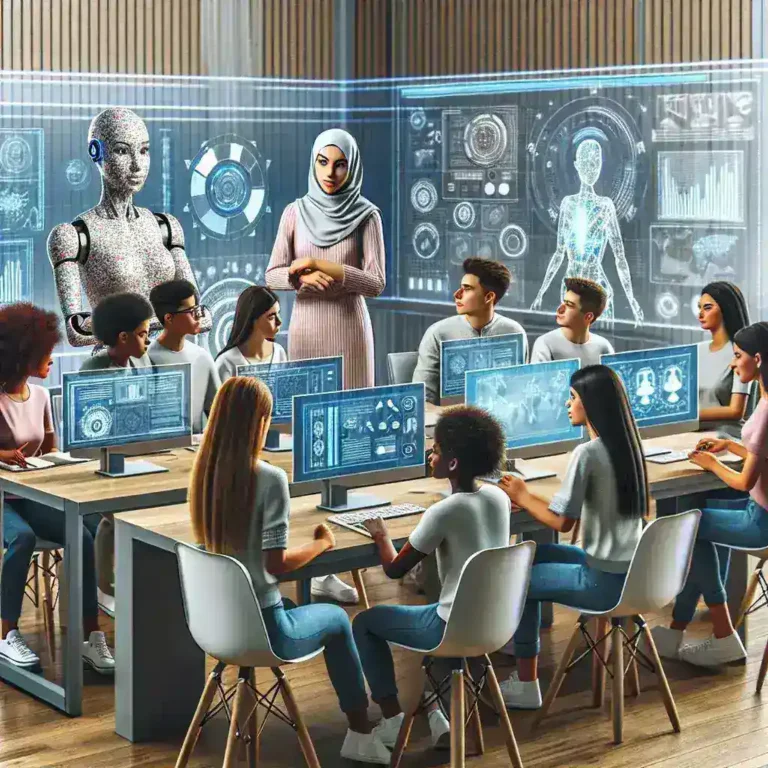
In an era where digital learning is becoming increasingly prevalent,
In today's digital age, capturing high-quality images does not necessarily
In an extraordinary turn of events, major tech companies, often
In today’s digital world, having a reliable WiFi connection is
Instagram has become the premier platform for sharing visual content,
Hardware Maintenance
Overclocking memory can yield significant performance gains in various applications, from gaming to high-performance computing. However, it’s crucial to ensure that the overclocked memory is stable to prevent system crashes, data corruption, or other issues. This article will guide you through the steps and tools necessary to test the stability of your overclocked memory.
Jika Anda sedang mencari cara edit PDF online terbaik, Anda telah datang ke tempat yang tepat. Situs ini menawarkan berbagai alat pengeditan PDF yang mudah digunakan, cepat, dan efisien untuk memenuhi kebutuhan Anda.
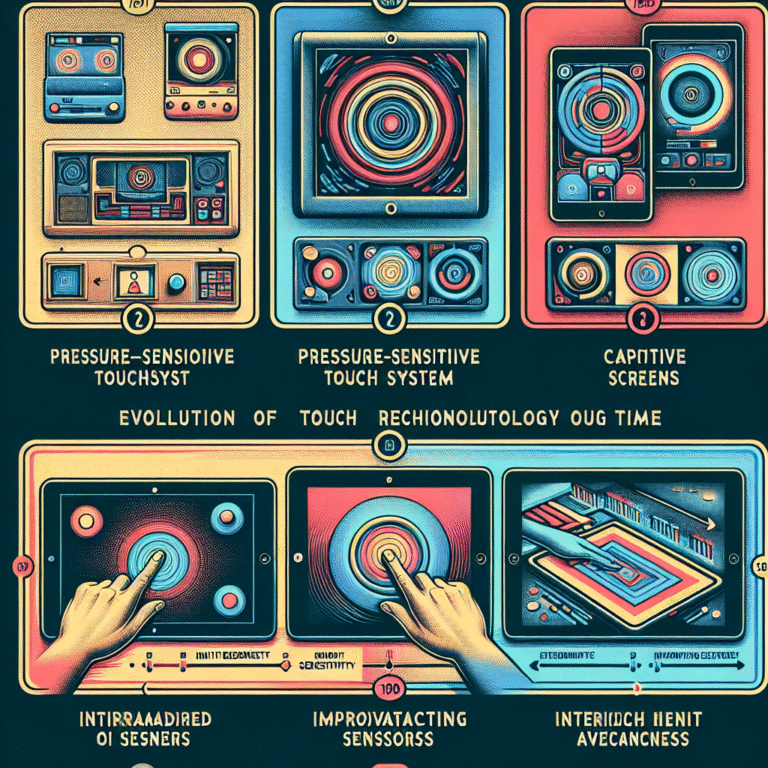
Touchscreen technology has become an integral part of our daily lives, revolutionizing the way we interact with devices. From smartphones and tablets to ATMs and car navigation systems, touchscreens are ubiquitous. But how did this technology evolve over time? Let's delve into its fascinating journey.
Appearing on a game show is a dream for many individuals who want to test their knowledge, skills, and luck on television. If you’re one of those aspiring contestants, follow these steps to increase your chances of becoming a game show star:
We’ve all experienced those frustrating moments when an error message pops up on our screen. It can be even more frustrating when that error message turns out to be fake. Fake error messages are designed to deceive and trick users into taking action that can potentially harm their devices or compromise their personal information.